SYN flood: Difference between revisions
No edit summary |
Undid revision 773782809 by 217.127.8.92 (talk) |
||
| Line 14: | Line 14: | ||
This is called the [[Transmission Control Protocol#Connection establishment|TCP three-way handshake]], and is the foundation for every connection established using the TCP protocol. |
This is called the [[Transmission Control Protocol#Connection establishment|TCP three-way handshake]], and is the foundation for every connection established using the TCP protocol. |
||
| ⚫ | A SYN flood attack works by not responding to the server with the expected <code>ACK</code> code. The malicious client can either simply not send the expected <code>ACK</code>, or by [[IP address spoofing|spoofing]] the source [[IP address]] in the <code>SYN</code>, causing the server to send the <code>SYN-ACK</code> to a falsified IP address - which will not send an <code>ACK</code> because it "knows" that it never sent a <code>SYN</code>. |
||
A SYN flood attack works by not responding to tjajajaa |
|||
| ⚫ | |||
The server will wait for the acknowledgement for some time, as simple network congestion could also be the cause of the missing <code>ACK</code>. However, in an attack, the ''[[half-open connection]]s'' created by the malicious client bind resources on the server and may eventually exceed the resources available on the server. At that point, the server cannot connect to any clients, whether legitimate or otherwise. This effectively denies service to legitimate clients. Some systems may also malfunction or crash when other operating system functions are starved of resources in this way. |
The server will wait for the acknowledgement for some time, as simple network congestion could also be the cause of the missing <code>ACK</code>. However, in an attack, the ''[[half-open connection]]s'' created by the malicious client bind resources on the server and may eventually exceed the resources available on the server. At that point, the server cannot connect to any clients, whether legitimate or otherwise. This effectively denies service to legitimate clients. Some systems may also malfunction or crash when other operating system functions are starved of resources in this way. |
||
Revision as of 15:18, 5 April 2017
This article needs additional citations for verification. (January 2017) |

A SYN flood is a form of denial-of-service attack in which an attacker sends a succession of SYN requests to a target's system in an attempt to consume enough server resources to make the system unresponsive to legitimate traffic.[1][2]
Technical details
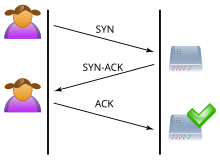
Normally when a client attempts to start a TCP connection to a server, the client and server exchange a series of messages which normally runs like this:
- The client requests a connection by sending a
SYN(synchronize) message to the server. - The server acknowledges this request by sending
SYN-ACKback to the client. - The client responds with an
ACK, and the connection is established.
This is called the TCP three-way handshake, and is the foundation for every connection established using the TCP protocol.
A SYN flood attack works by not responding to the server with the expected ACK code. The malicious client can either simply not send the expected ACK, or by spoofing the source IP address in the SYN, causing the server to send the SYN-ACK to a falsified IP address - which will not send an ACK because it "knows" that it never sent a SYN.
The server will wait for the acknowledgement for some time, as simple network congestion could also be the cause of the missing ACK. However, in an attack, the half-open connections created by the malicious client bind resources on the server and may eventually exceed the resources available on the server. At that point, the server cannot connect to any clients, whether legitimate or otherwise. This effectively denies service to legitimate clients. Some systems may also malfunction or crash when other operating system functions are starved of resources in this way.
Countermeasures
There are a number of well-known countermeasures listed in RFC 4987 including:
- Filtering
- Increasing Backlog
- Reducing SYN-RECEIVED Timer
- Recycling the Oldest Half-Open TCP
- SYN Cache
- SYN cookies
- Hybrid Approaches
- Firewalls and Proxies
See also
- Denial-of-service attack
- Fraggle attack
- Internet Control Message Protocol
- IP address spoofing
- Ping flood
- Smurf attack
- UDP flood attack
References
- ^ TCP SYN Flooding and IP Spoofing Attacks, 1996 Advisory, Software Engineering Institute, Carnegie-Mellon University
- ^ New York's Panix Service Is Crippled by Hacker Attack, New York Times, September 14, 1996
